April 1st fades away, and with it, the harmless jokes and false announcements that make you double-check everything on April Fools' Day disappear too.
But scammers? They never take a break.
Spring ranks among the busiest seasons for cybercriminals. It's not due to negligence but because people are often distracted, juggling tasks swiftly, making it easier for seemingly credible threats to slip past unnoticed during a busy workday.
Here are three current scams targeting diligent, well-intentioned employees just trying to navigate their daily tasks.
As you review these, ask yourself: Does everyone on my team pause long enough to recognize these risks?
Scam #1: Fake Toll or Parking Fee Alerts via Text
An employee receives a text like this:
"You owe $6.99 in unpaid toll fees. Pay within 12 hours to avoid penalties."
The message references an authentic toll system — E-ZPass, SunPass, FasTrak — matching the employee's location. The small amount doesn't raise suspicion. Between meetings, they click the link, pay quickly, then move on.
But that link is bogus.
In 2024 alone, the FBI logged over 60,000 reports of fake toll-text scams, with incidents surging 900% into 2025. Hackers have created more than 60,000 counterfeit domains mimicking real toll authorities — a clear sign of this scam's profitability. Some messages even target people in states without toll roads.
Why does this work? Because a small charge feels harmless, and many people have recently encountered tolls or parking so the alert seems legitimate.
Protection strategy: Authentic toll agencies never demand immediate payment through text. Smart companies establish a rule: Payments are never made via SMS links. If in doubt, employees should independently visit official websites or apps to verify charges, and never respond to such texts — even saying "STOP" confirms the number is active, inviting more fraud.
Quick convenience is the bait; strict procedures are your shield.
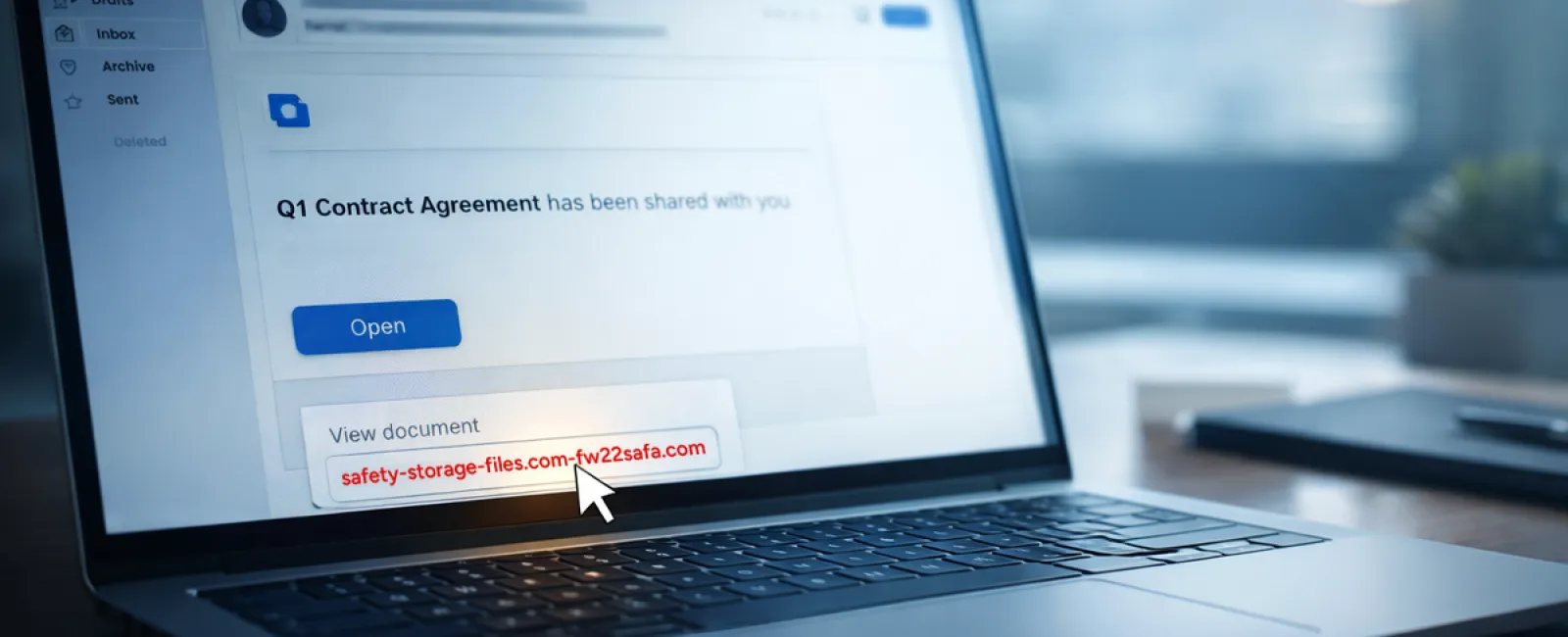
Scam #2: "Your File Is Ready" Email Traps
This scam blends seamlessly into typical work routines.
An employee is sent an email claiming a document was shared with them. It often appears as a contract via DocuSign, a spreadsheet on OneDrive, or a Google Drive file.
The sender's name looks legitimate, and the email formatting matches usual file-share notifications.
Upon clicking, the employee is prompted to log in and inadvertently enters their work credentials.
Now hackers have access to the company's cloud environment.
Such phishing has surged dramatically. In 2025, attacks exploiting trusted platforms like Google Drive, DocuSign, Microsoft, and Salesforce jumped by 67%, according to KnowBe4's Threat Labs. Google Slides phishing links soared over 200% in just six months.
Employees are also seven times more likely to click malicious links in apps like OneDrive or SharePoint compared to random emails, because these notifications appear authentic.
Advanced scammers even craft files within compromised accounts and use genuine sharing features, so emails originate from official Google or Microsoft servers. Spam filters don't catch them, since they're technically legitimate alerts.
Protection strategy: Train employees to avoid clicking unexpected file-share links in emails. Instead, they should log into these platforms directly via a browser to verify files. Organizations can swiftly reduce risk by restricting external sharing and enabling alerts for suspicious login activities — settings achievable within 15 minutes by IT teams.
Simple habits yield powerful security.
Scam #3: Expertly Written Phishing Emails
Gone are the days when phishing emails were riddled with errors and obvious mistakes.
Today, AI-generated phishing emails outperform human-written ones, with a 54% click rate versus 12%, based on a 2025 academic study. They skillfully reference real company names, job titles, and workflows, scraping publicly available info within seconds.
These attacks target departments thoughtfully: HR and payroll receive fake employee verifications; finance departments get vendor payment change requests. One test found 72% of employees engaged with vendor impersonation emails — 90% more than other phishing types. These messages are calm, professional, and urgent without sounding alarmist, mimicking a normal workday inbox.
Protection strategy: Any request involving credentials, payment updates, or sensitive data must be confirmed through a second channel—phone, chat, or face-to-face. Employees also should hover over sender addresses to verify domains before clicking. If a message pressures urgency, treat that as a red flag.
True cybersecurity fosters caution without panic.
The Bottom Line
These scams exploit familiarity, authority, urgency, and the urge to act quickly.
The real vulnerability isn't careless staff but systems that expect everyone to always pause, double-check, and respond perfectly under pressure.
When a rushed click can disrupt your day, it's not a personnel problem — it's a process failure.
And the good news? Processes can be fixed.
How We Support You
Most business owners don't want cybersecurity to become another burden or be the sole trainers on what to avoid clicking.
They want assurance their company isn't unknowingly at risk.
If you're worried about your team's security — or know another business leader who should be — let's talk.
Schedule a candid discovery call where we'll explore:
- Current threats facing businesses like yours
- How vulnerabilities appear during routine work
- Practical, efficient steps to minimize risk without slowing your team
No pressure. No scare tactics. Just honest conversation about protecting your business.
Click here or give us a call at (949) 396-1100 to schedule your free 15-Minute Discovery Call.
If this message isn't for you, feel free to forward it to someone who'd benefit. Sometimes, recognizing risks converts a "near miss" into a "blocked threat."